While understanding EU regulation CRA, I came to know about EUVD in Q1 2025. This blog is about my understanding of EUVD. I personally think this is a really good initiativ. Specially considering In April 2025 there were reports of funding issues to CVE from MITRE came out.
Apparently EUVD originates from NIS2 directive (another regulation in EU) for critical infrastructure in EU. Infact as per the NIS2 Directive, ENISA (EU Agency for Cybersecurity)is mandated to develop and maintain the European vulnerability database.
As per EUVD website:
CVE data, data provided by ICT vendors disclosing vulnerability information via advisories, and relevant information such as CISA’s Known Exploited Vulnerability Catalogue are automatically transferred into the EUVD. This will also be achieved with the support of Member States who established national Coordinated Vulnerability Disclosure (CVD) policies and who designated one of their CSIRTs as the coordinator, ultimately making the EUVD a trusted source for enhanced situational awareness in the EU.
To avoid efforts duplication and to support complementarity, ENISA closely cooperates with MITRE and European as well as non-European operators of the Common Vulnerabilities and Exposures (CVE) system. In this context, ENISA offers vulnerability registry services after its onboarding as a CVE Numbering Authority (CNA), with a focus on vulnerabilities in IT products discovered by or reported to European CSIRTs for coordinated disclosure.
Above two points clarify about how does EUVD works. It is important that EUVD cooperates with MITRE and others EU and non-eu operators of CVEs.
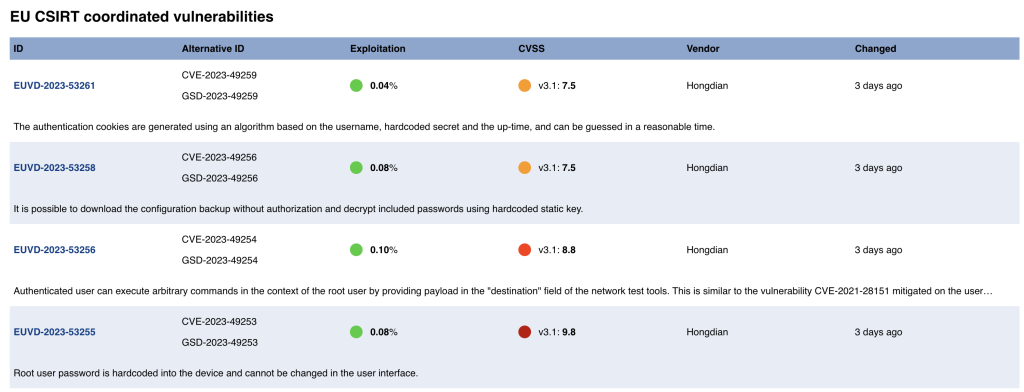
It is still too early for EUVD, it will be interesting to see how to future unfolds. Im interested in coordinated disclosure from various member sates of EU.
Furthermore, EUVD service retrieves its data by querying the Vulnerability-Lookup collection, enriches the data, and assigns a unique EUVD identifier (on top of existing identifiers such as CVE) to each vulnerability record.
The EUVD builds on the existing CVE system: vulnerabilities that qualify for a CVE get one as usual. EUVD then adds extra details and assigns its own EUVD ID to new entries. For easy cross-referencing, each listing includes the CVE and any other relevant vulnerability IDs when available.
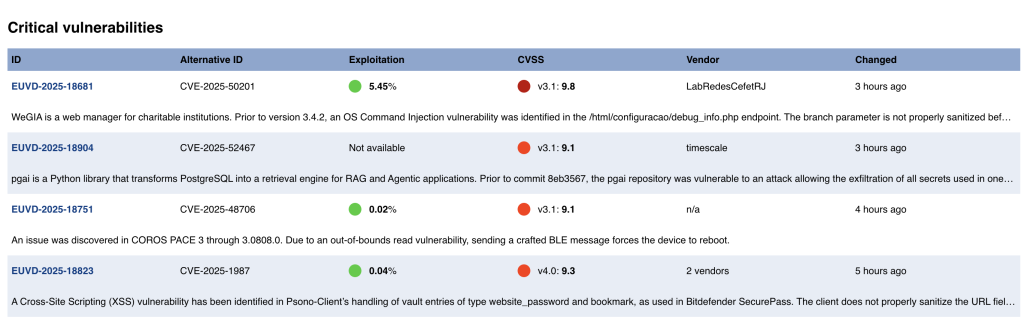
API endpoints are available at https://euvdservices.enisa.europa.eu/api/<endpoints> for example one endpoint fetching critical vulnerabilities is https://euvdservices.enisa.europa.eu/api/criticalvulnerabilities. Api doc is present at https://euvd.enisa.europa.eu/apidoc.
Critical vulnerabilities view as shown below is very straight forward. Interesting column is exploitation. As I understand this is EPSS(Exploit Prediction Scoring System) score. EPSS score predicts chances of exploiting a vulnerability in next 30 days. Reason these vulnerabilities are critical is by their CVSS score of more than 9.
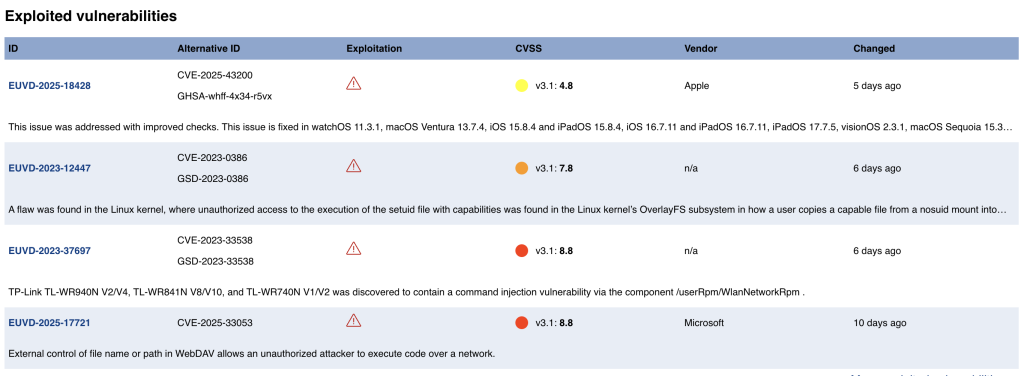
Below is view for exploited vulnerabilities. Important column here is exploitation. Here information form CISA KEV (known exploited vulnerabilities) is used to tell if the vuln is being exploited. Important point to note here is no EPSS score is used, as the vulns are being exploited already.
While one can see mapping between EUVD and alternative ID. Alternative ID is CVE ID. There could be multiple alternative ID like from CVE and GSD (Global security database).
Now the last view about EU CSIRT coordinate vulns particularly by EU CSIRT network. This is interesting because the disclosure and remediation process has been actively coordinated by European CSIRTs.
When I started writing this blog I had questions related to working of EUVD. While I researched more about this topic then it became clearer that EUVD is a collaboration effort. Time will tell success of this initiativ specially thinking from CRA prespectiv.
